Security breaches have become increasingly common, causing organizations to seek a proactive approach to protect their sensitive information. The increasing number of cyber attacks, data breaches, and security vulnerabilities have exposed organizations to significant financial, legal, and reputational risks.
However, the traditional approach of securing systems post-development is no longer sufficient to safeguard against the evolving nature of modern-day cyber threats.
To mitigate these risks, it is essential to implement effective security measures that provide comprehensive protection throughout the development cycle. That’s where “Security as Code(SaC)” emerges as a viable solution to address the growing security concerns.
In this blog, we’ll discuss what exactly SaC is, its aspects, and some best practices.
What is SaC?
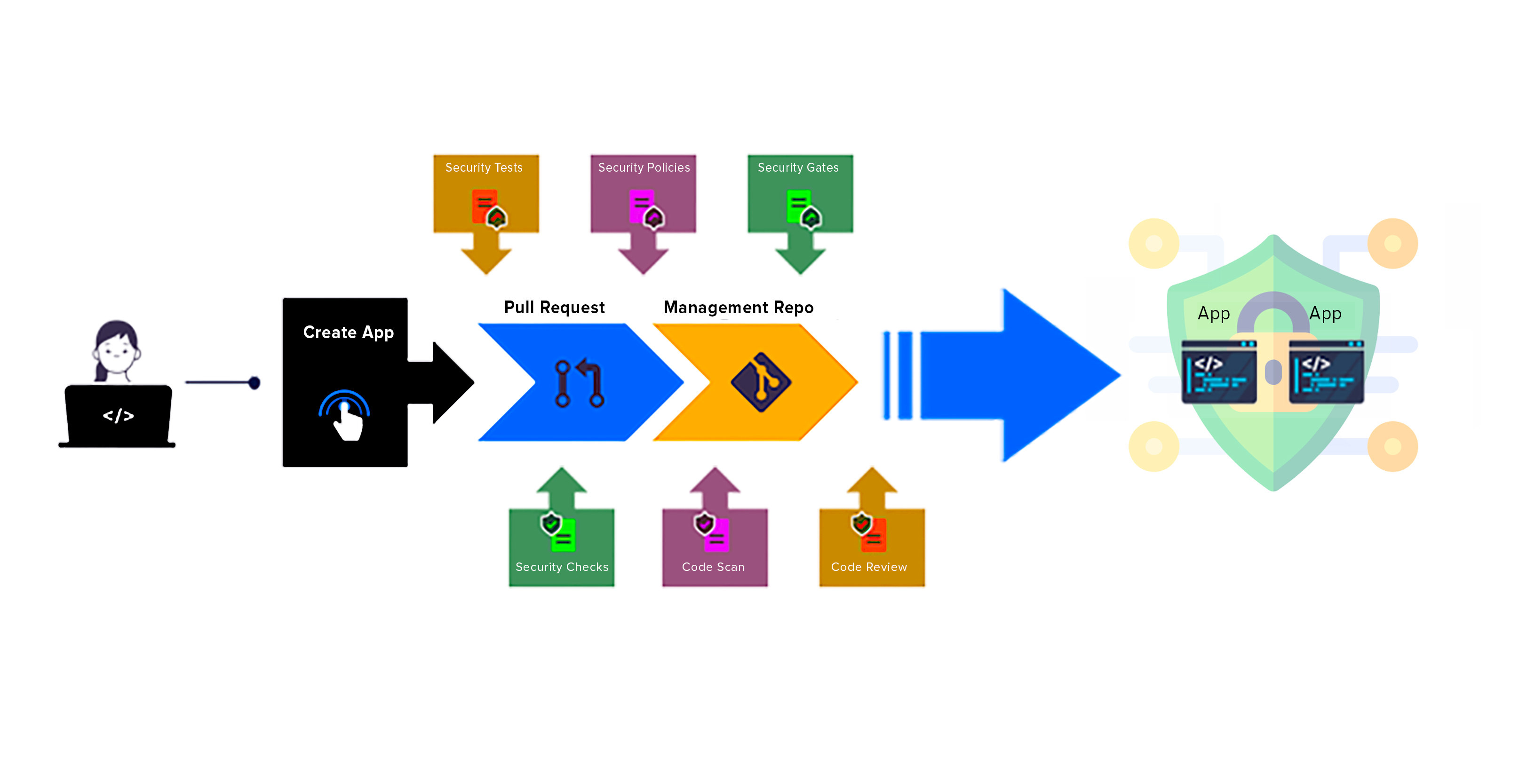
SaC refers to the practice of seamlessly integrating security measures into the DevOps workflow. It involves identifying opportunities to include security checks, policies, tests, and gates without incurring slowdowns or extra expenses in the code and infrastructure modification process.
This enables developers to build more secure software and applications, without having to compromise on functionality or performance.
Moreover, it allows for continuous security monitoring and rapid response to security incidents, reducing the impact of cyber-attacks and other security threats. This also helps organizations achieve greater transparency in their risk management system, allowing them to identify and address potential security threats before they can be exploited.
Some Important Aspects of SaC
Security testing
Security Testing involves identifying and mitigating security vulnerabilities in software applications, systems, and networks. This includes scrutinizing the features and code to detect vulnerabilities that could compromise its confidentiality, integrity, or availability.
While many view security testing as a measure to prevent attacks, it also includes detecting accidental malfunctions, data breaches, and other non-attacker-related security issues. By implementing security standards and adhering to them through security testing, organizations can ensure that their application remains secure and protected from any security concerns.
Vulnerability Scanning
Vulnerability scanning is a pivotal step in securing your system or application, aiming to identify and remediate security weaknesses that could be exploited by malicious actors. This process is crucial in safeguarding your organization's assets and sensitive information.
It involves regularly scanning every component in your application and deployment for known vulnerabilities at every stage of its life cycle. These scans can help you identify common vulnerabilities such as SQL Injection, Cross-site scripting, and others, which are frequently targeted by attackers.
Regular updates and fixes will likely reduce the number of vulnerabilities detected by these scans. Therefore, it's critical to perform continuous and automatic scanning of test, staging, and production environments, and to examine containers for compliance with best practices and vulnerabilities in specific packages.
ALSO READ: A DevSecOps Checklist to Secure DevOps Pipeline
Access control and policy management
As the complexity of applications continues to grow, so does the potential for things to go wrong. In particular, applications that handle custom requirements and user-specific data need to be protected from unauthorized access or malicious activity. Access control and policy management play a vital role in securing such applications.
Access control refers to the process of restricting user access to specific resources or functionalities within an application. Policy management involves setting up rules and guidelines that dictate how user access is granted or denied. These processes formalize governance decision-making and ensure that compliance with established policies is enforced.
This approach enables the organization to move more quickly, without jeopardizing essential security and compliance requirements. It also allows for transparency and direct communication between teams, ensuring that any issues or discrepancies are addressed promptly.
Common Security Risks at the Code Level
1. Injection attack: This occurs when an attacker injects malicious code into an application, such as SQL, NoSQL, or OS commands, to gain unauthorized access to data. This can lead to data breaches, system crashes, and other security incidents.
2. Cross-site scripting (XSS): XSS attacks occur when an attacker injects malicious scripts into a web application, which can then execute in the user's browser, allowing the attacker to perform malicious actions. This can result in the compromise of user accounts, theft of sensitive data, and other security incidents.
3. Buffer overflow: Buffer overflow occurs when an application tries to store more data in a buffer than it can handle, causing the excess data to overflow into adjacent memory locations. This can result in the program behaving unexpectedly, crashing, or being vulnerable to attackers who can exploit the overflow to execute arbitrary code.
4. Denial of Service (DoS) attacks: A DoS attack can overload a system with requests, making it unavailable to legitimate users. This can be achieved by exploiting vulnerabilities in the code, such as by sending malformed packets or by repeatedly requesting expensive operations.
5. Insecure deserialization: This is the process of converting data from a serialized format into an object in memory. If the input data is not properly validated, attackers can send malicious input data that can cause the application to execute arbitrary code, resulting in data theft or system compromise.
6. Broken authentication and authorization: This happens when an application does not properly authenticate and authorize users. It allows attackers to gain unauthorized access to sensitive data or conduct other malicious activities.
ALSO READ: A CTO's Guide to DevOps and its Services
Best Practices While Implementing SaC
Implementing Security as Code (SaC) requires a structured approach and adherence to best practices to ensure that security measures are effectively integrated into the software development process. There are several key best practices that should be considered, including:
1. Security requirements: Begin by identifying the security requirements that are specific to the organization, the software application, and its users. This includes assessing security risks and vulnerabilities, regulatory requirements, and compliance standards.
2. Embedding security measures: Security measures should be embedded early in the SDLC, from design to deployment, to ensure developers can build secure applications.
3. Utilizing automation tools: Automation tools should be employed to identify security vulnerabilities, scan code for potential threats, and automate testing and deployment processes.
4. Secure coding practices: Developers should be trained in secure coding practices, such as input validation, error handling, and encryption, to ensure that the code is secure from the outset.
5. Regular security testing: Regular security testing, including vulnerability scanning and penetration testing, should be conducted to identify and remediate any vulnerabilities or weaknesses.
6. Audit trail: An audit trail of all changes made to the software application, should be maintained to ensure accountability and traceability.
7. Continuous improvement: Regular reviews and evaluations of the effectiveness of implemented security measures should be conducted to ensure that security remains up-to-date and effective.
The New Normal - Secure Your Applications with SaC
SaC is a critical methodology for businesses seeking to build and maintain secure applications. By integrating security practices and measures into every stage of the SDLC, organizations can create a culture of shared responsibility for security and stay ahead of emerging threats.
This approach enables security teams to work in collaboration with developers and operations teams, streamlining the development process and ensuring that security is not an afterthought but rather an integral part of the development process. With its focus on automation, continuous testing, and feedback loops, it helps businesses achieve faster time-to-market and maintain the trust of their customers.
Don't let cyber threats disrupt your business. Check out our DevOps services and book a free consultation with our experts. Our dedicated team provides solutions that can help you minimize system downtime and protect your valuable data.




